Eclipse Corporation, provider of DocOrigin, an enterprise forms, documents and customer communications software solution, announced today the 5 year anniversary of working with their OEM customer, Advantage 360, through their partner ProTechnology, Inc.
Advantage 360 (A360) is a leading provider of customer care and billing systems for the Telecom industry, providing convergent billing for wired, wireless, internet, and satellite services. They have a global customer base ranging from North America to Mali to the Caribbean with installations in 200+ customers in more than 30 countries. In 1999, A360 needed a document and forms generation solution embedded in their software. Working with ProTechnology, A360 selected a tier one provider of forms software, which in the 90s met there needs. Unfortunately, the technology was sunset and the replacement software from the original vendor was much more complex, expensive and would not perform as well as the software they had been using.
In 2012, A360 was in need of a replacement for the sunset Adobe Central product so they went to their trusted partner, ProTechnology. Dan Roth, CTO and founder of ProTechnology introduced them to DocOrigin. Bob Hennemann, CFO at Advantage 360, said selecting DocOrigin and ProTechnology was a “no brainer”, they continue to expand the use of DocOrigin to improve omni-channel communications with clients.
After OEM’ing DocOrigin for 5 years, Advantage 360 couldn’t be happier and all new customers receive DocOrigin as an integral solution with the OS360 software from Advantage 360. Hennemann says, “DocOrigin is much easier to implement and the time it takes to develop and maintain forms for customers has decreased significantly. The learning curve to use DocOrigin is much faster and training customers has become easier. Our staff is very happy with DocOrigin. The best part is that as the product has improved over the years, with upgrades and updates, it’s made form development even easier. The fantastic support we have received from both ProTechnology and Eclipse has enabled us to quickly and easily resolve all issues and challenges we have encountered and we have had no production failures. Reliability is not an option in the Telco industry. We see a bright future ahead with ProTechnology and Eclipse!”
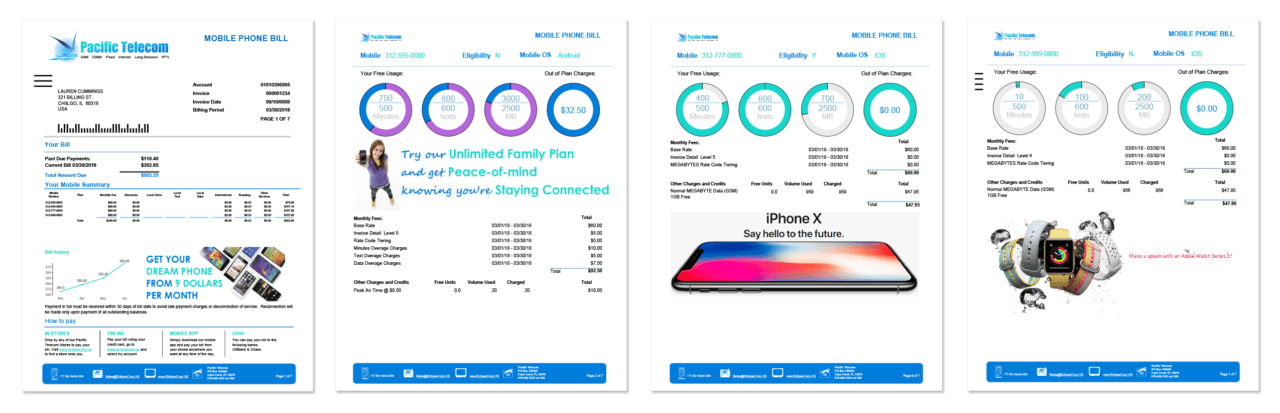
“DocOrigin improves Advantage 360’s products by simplifying their software development processes and allowing for much easier design and deployment. Plus, the omni channel communication delivery features, like print, email, web, XML, cloud fax, SMS, portals and more, have increased the value of the A360 offering to their clients. DocOrigin gives them a major advantage to compete in a global market.” said Eclipse CEO, Steve Luke.
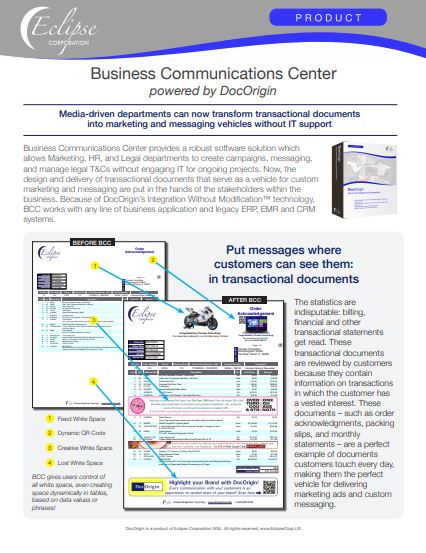
The future is indeed bright! Hennemann is excited about DocOrigin’s solutions for Dynamic Business Documents and Business Communications Center. He says, “DocOrigin has been meeting all of our needs and they are ahead of the curve in releasing new features. The reliability, performance and features of DocOrigin continues to prove we made the right choice.”
About Eclipse Corporation
A leading provider of enterprise document composition, presentation, automation and customer communications management software. Eclipse and it’s partners works closely with clients to provide tailored solutions that conform to specific needs at a fair price.
DocOrigin, Business Communications Center and Dynamic Business Documents
About Advantage 360
Since 1984, Advantage 360 has developed and continually evolved forward-thinking carrier-grade billing, POS, CRM and operational support software that is designed to reach well beyond their customers to their customer’s customers, and to provide an exceptional experience at every level.
About ProTechnology, Inc.
Founded in 1996, ProTechnology has delivered and supported enterprise forms and communications software solutions for hundreds of customers. ProTechnology provides complete solutions for document design, workflow and ECM. From evaluations, design and implementation to annual support we take care of our customers for the life of their requirements.